Download Microsoft.owin.security.cookes
Jul 03, 2013 Last week Microsoft released the preview of Visual Studio 2013, and along with it came the ASP.NET and Web Tools for Visual Studio 2013 Preview. In this new release, Javier Calvarro Nelson July 5, 2013. How does VS determine which version of Razor engine to use when editing razor webpage files. C# (CSharp) Microsoft.Owin.Security.Cookies CookieAuthenticationProvider - 6 examples found. These are the top rated real world C# (CSharp) examples of Microsoft.Owin.Security.Cookies.CookieAuthenticationProvider extracted from open source projects. You can rate examples to help us improve the quality of examples.
Mar 10, 2016 Using OWIN and Active Directory to authenticate users in ASP.Net MVC 5 application Posted on March 10, 2016 October 27, 2016 by trailmax UPD There is a part 2 of this blog-post explaining how to do roles and fixing a minor issue with authentication.
Oct 10, 2015 In older version of ASP.NET applications used the FormsAuthentication module to issue Cookies to identify the current logged in user. The cookie authentication is now handled by the Microsoft.owin.Security.Cookies middleware. We use extension method UseCookieAuthentication to configure this middleware. 19 rows Oct 27, 2015 Thread Safety. Any public static (Shared in Visual Basic) members of. Feb 08, 2017 Katana provides cookie middleware to serialize user principal into an encrypted cookie and the cookie is used to validate the authenticated user in subsequent request. This post will take a look at Katana’s cookie authentication implementation and see the machine key’s role in this procedure. The sample used in this post is one ASP.NET MVC5. Feb 10, 2017 Katana is a flexible set of components for building and hosting OWIN-based web applications on.NET Framework. This repo is the home for the Katana host, server, and middleware source code and documentation. Official releases of Katana components (including prerelease versions) can be found on https.
-->
Katana provides cookie middleware to serialize user principal into an encrypted cookie and the cookie is used to validate the authenticated user in subsequent request. This post will take a look at Katana's cookie authentication implementation and see the machine key's role in this procedure. The sample used in this post is one ASP.NET MVC5 application created by Visual Studio 2015 Update 3.
After we use web browser to login one form authentication website, we will be able to login automatically next time even reboot the web browser or reboot the machine. Actually, for most commercial web site, even the web server is rebooted, the end user's experience is the same. All of these benefit from cookie and the machine key sit behind (or similar encrypt approach).
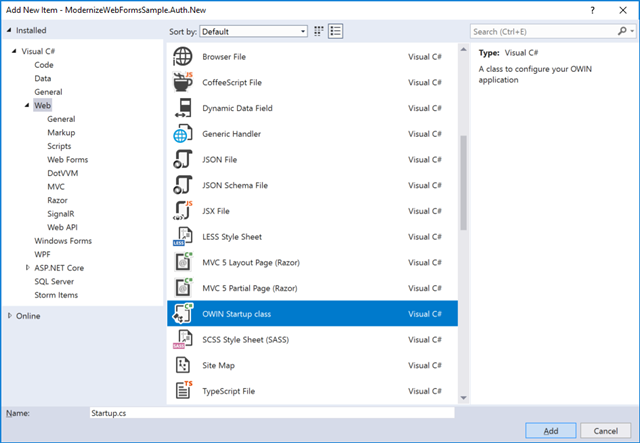
Katana has implemented claims-based authentication based on cookie via CookieAuthenticationMiddleware in Microsoft.Owin.Security.Cookies module, it is injected into the Owin pipeline via UseCookieAuthentication. In the same module, CookieAuthenticationHandler class is used to manipulate the cookie:
- ApplyResponseGrantAsync: write encrypted cookie into http response.
- AuthenticateCoreAsync: retrieve the cookie from request, decrypt the cookie and generate the claims.
But how the cookie is encrypted? It is controlled by TicketDataFormat which is a field of CookieAuthenticationOptions when configuring the authentication behavior.
Basically, TicketDataFormat has three fields to define how to encrypt, encode and serialize the cookie shown below.
Owin Cookie Expiration
In the above, Microsoft.Owin.Host.SystemWeb.DataProtection.MachineKeyDataProtector object is the wrapper class to perform the real encryption operation. In http://katanaproject.codeplex.com/SourceControl/latest#src/Microsoft.Owin.Host.SystemWeb/DataProtection/MachineKeyDataProtector.c (shown below), we can clearly see it is using machine key to protect the claim, thus, in order to make web application work in a web farm environment, if the session is not stick to a web server, machine key must be the same between each web server to make sure same cookie can be extracted by different server. Notice that _purposes must be the same to make sure protect and unprotect can work well with each other.
In the following, I have composed a sample code to simulate how claims are extracted from a cookie. I just copy the first two classes from Katana source code repository because they are implemented as internal.
Microsoft Owin Security Google

Cookie is convenient for the authentication process, while in default Katana implementation, it only checks whether the cookie is valid while not verify whether the corresponding user really exists in the user store. So, suppose one end user has valid cookie in multiple devices, then he removes his account from one of the device. How to use vst crack. Now, his account doesn't exist anymore in the corresponding web site, while he will still be able to login from other devices until the cookie is expired. Though not many web sites provide account remove functionality, it is a good design to valid the user during the login via OnValidateIdentity. The below sample code will reject jacky@contoso.com's login request.
Microsoft.owin.security.oauth.dll Download
In ASP.Net Core, by default, whether it is machine key or DPAPI used to protect the cookie is determined by whether the application is running on ASP.NET or in a different process, you may also have a check on CookieAuthenticationOptions. Notice that ASP.Net MVC and ASP.Net Core applications can share cookie as well, please refer to Sharing cookies between applications for more introduction on it.